Anti-Fraud, Metrics Set Up
THIS ARTICLE IS NOT UPDATED. WE ARE ON THE INTERCOM NOW!
http://help-center.peerclick.com/en
JOIN US THERE AND WATCH ALL UPDATED PEERCLICK GUIDES!
What is it Anti-Fraud?
This feature uses the predefined list of metrics that helps you to identify invalid traffic. Any event that matches criteria in at least one of the metric is considered to be suspicious.
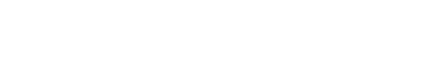
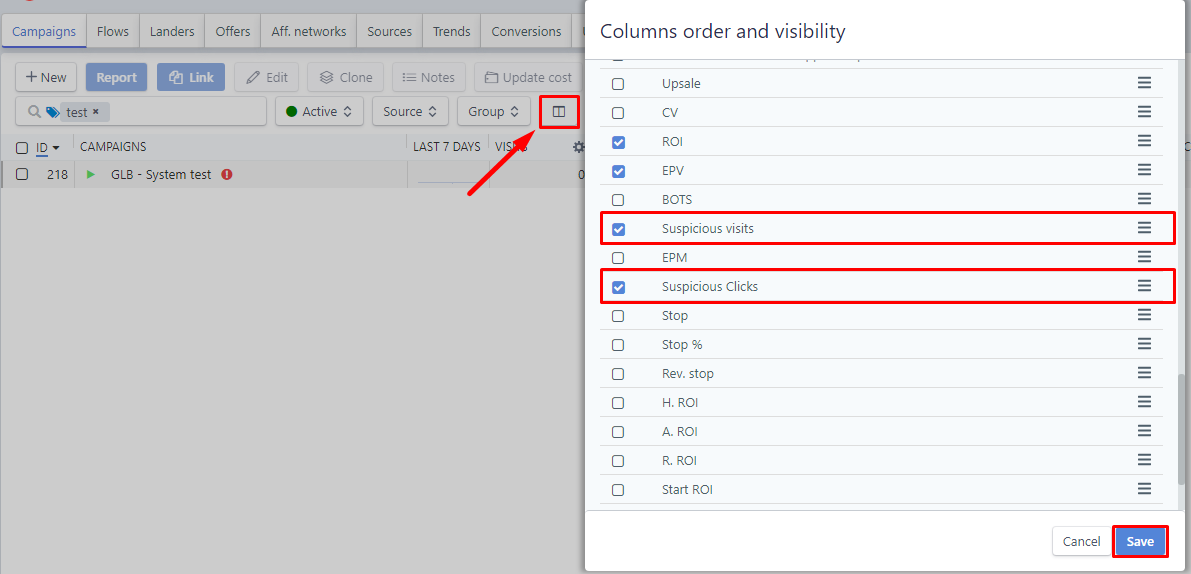
Suspicious events, divided into clicks and visits, are presented in two columns for every campaign element and on every drill-down level.
Checking your traffic
The Anti-Fraud metrics show you what portion of your traffic is considered to be suspicious. Traffic is divided in two categories:
-
Suspicious visits. Shows the percentage of visits flagged by at least one metric as suspicious.
-
Suspicious clicks. Shows the percentage of clicks flagged by at least one metric as suspicious. Clicks are visible only if you use landing pages in your campaign funnels.
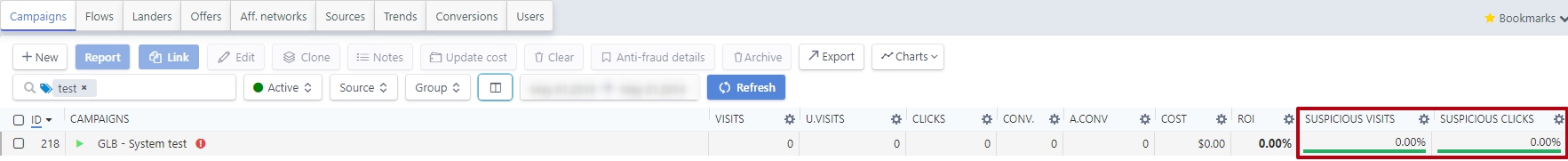
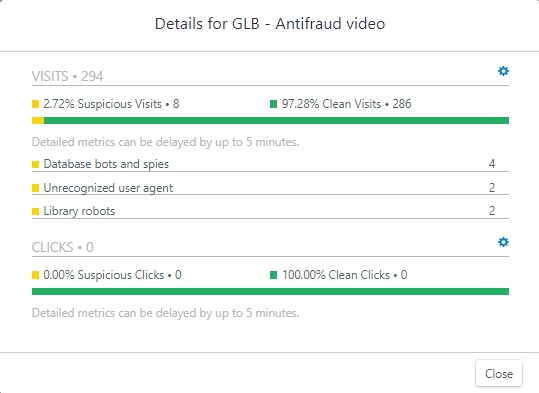
Checking detailed traffic stats
You can open a detailed view to see which metrics tagged traffic. That will allow to highlight suspicious in your traffic, which in turn will give you the opportunity to stop this traffic directly on the traffic source platform.
To do so, perform the following steps:
- Select the campaign element that you want to see detailed stats for.
- Click the Anti-fraud details button.
PeerCLick Info
Mind that the detailed view shows data that may be delayed up to 5 minutes due to processing requirements. The events are flagged independently of each other, meaning that the same event might be flagged based on several metrics. Thus, the overall number of flagged events based on the detailed metrics might be higher than the total number of clicks or visits.
You can turn select and deselect metrics to be used for checking incoming traffic. This will affect how your data is calculated and presented in the Anti-Fraud Details pop-up window and in the following columns:
- Suspicious visits
- Suspicious clicks
PeerCLick Info
Changing Anti-Fraud Metrics settings causes the incoming traffic characteristics will be checked against newly set options. Past suspicious traffic values will NOT be recalculated with those settings.
Configurating Anti-Fraud Metrics
You can select which metrics should be used to check incoming traffic for suspicious visits and clicks. To configure Anti-Fraud Metrics, perform the following steps:
- In PeerClick, click the Settings --> go to the Anti-Fraud tab
- Tick the checkboxes next to the metric names that you want to use for checking your traffic.
- Click the Save button.
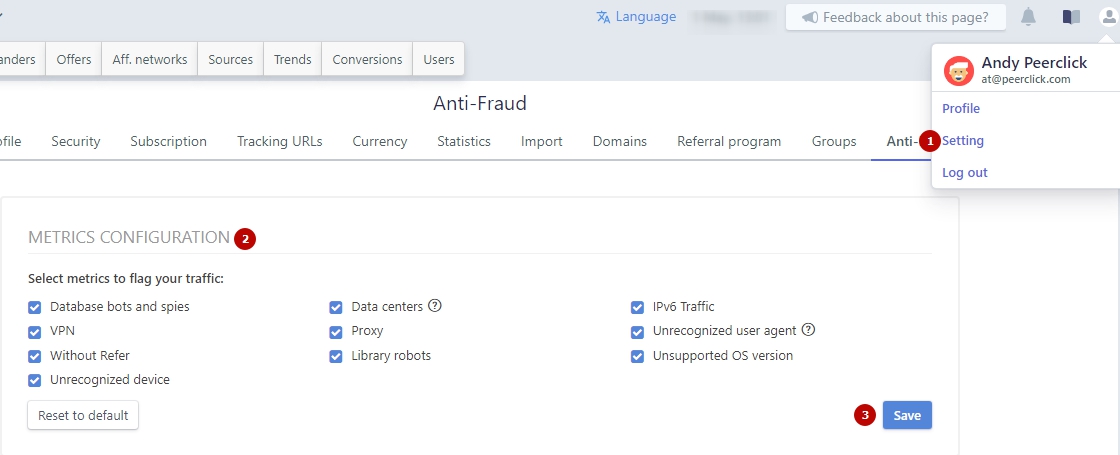
From now on your traffic is checked using newly set metric selection.
Metrics List
PeerClick uses different metrics to scan incoming traffic. When criteria set in those metrics are matched, such an event, be that either click or visit, is then flagged as suspicious. Those flags represent characteristics that usually accompany the invalid traffic. Read below about metrics used and decide whether this kind of traffic is wanted in your funnels.
Database bots and spies
Own and third-party databases of bots and spies. Keep in mind that not all bots have bad intentions. Some of them follow the links in the funnels of your campaign only for indexing the contents of a web page. PeerClick allows you to use these well-known friendly bots in your campaign funnel, but does not include the events generated by them in the reports. This means that your statistics are not distorted by them, and these events do not affect the limits of your tariff plan.
VPN and Proxy
Traffic using this kind of connection. People often use this technology to hide their location, bypass the blocking and are located on the Internet under a non own -IP address.
Without referrer
PeerClick gathers aggregated information about reputation of a referrer from different sources. Also registred visits with an empty and not passed referrer.
Unrecognized device
Traffic also carries identifiable information about a device or a program that is behind a visit. PeerClick with the help of a 3rd party service detects a user device. If a device cannot be recognized, such visit or click is then flagged.
Data Centers
PeerClick uses special sofware to identify if the IP address behind a visit or click is originated from known data centers. Data centers, such as Amazon Web Services, have their own batches of IP addresses assigned to them. Some of the data centers might be a source of invalid traffic but not all. For example, VPN users may be routed through data centers. So, a visit that came from an IP address associated with a data center does not necessarily mean that it is invalid, but it makes it more likely.
Library robots - Библиотека роботов
In this metric information about a user agent is taken into consideration, it flags traffic when a class of the user agent states it is a library. Library class may refer to PHP, Java or other programs that are behind a visit. They do not necessarily have malicious intent, they might be simply scanning website content for various reasons and generate traffic in this process.
Ipv6 Traffic
Internet protocol traffic version 6. At the moment, it is weakly distributed in the CIS, and is not used by private individuals, which increases the likelihood of such traffic belonging to bots.
Unrecognized user agent
User agent information should be passed in a proper format and most traffic follows this procedure. If there is a different format used in an event, it will be flagged with this metric.
Unsupported OS version
The information about visitor's operating system and its version can be also derived from a user agent. If a system is recognized as old and not supported for a very long time, it is unlikely it has a human origin Such visit is then flagged.
Updated almost 6 years ago